| Version 7 (modified by dabantz@…, 11 years ago) (diff) |
|---|
Two-factor Authentication
Two-factor authentication requires users to provide a "second factor" in addition to the correct password to authenticate and gain access to resources. If your password is "something you know", the second factor can be described as "something you have" such as your working telephone or smartphone. [In principle the second - or third - factor could be "something you are" such as fingerprint or voiceprint recognition.]
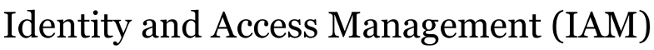
The UA Identity Provider is being extended to allow use of two-factor authentication using Duo Security. When two-factor authentication is invoked (as described below) you will first provide your identifier and UA Password just as you usually do for most applications. If and only if your password is verified a second screen will ask for the second factor. That second factor may be one of the following:
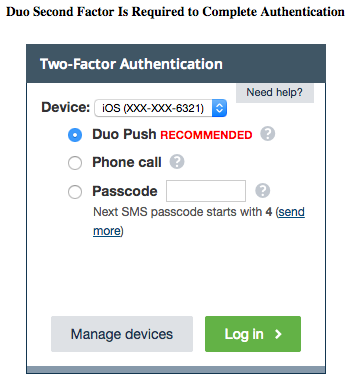
- replying "accept" in a request for access sent to a smartphone app on your registered phone
- entering a code sent via text to your registered cell phone
- entering a code your hear in a voice call to your registered phone.
Login page request after password verified, showing options available for 2nd factor
Any of those methods demonstrate you "have" the registered device or phone number. The smartphone app is generally regarded as the most convenient, as you do not have to type a code. Image of the Duo smartphone app showing request for login is below:
A one-time registration process records a user's phone number and preferred means of providing the second factor. That is, the initial registration associates a specific phone number and mode of communication with your UA Username or ID #. A single user may have multiple registered second factors; for example, you might have a smartphone that uses the Duo Security app and a land line on which you can receive a voice call providing a one-time code.
Invoking two-factor authentication
At least two means of invoking two-factor authentication are envisioned:
(1) A service can request two-factor authentication when relying on the Identity Provider to authenticate users. It does so by explicitly requesting the two-factor "authnContext" in its request. An important caveat is that the Identity Provider is not in general guaranteed to honor that request. The Identity Provider may not be capable of a particular method and default or fall back to some other method. The Identity Provider will include a precise indication of the method it did use to authenticate the user, but it is up the relying service to verify that the method used provided what that service considers an acceptable method and to respond accordingly. That is, the SP might deny access altogether if the the authentication method was not that requested, or it may allow access to some portion of the service.
(2) An individual user can require two-factor authentication for their identity. A user desiring higher assurance that others do not impersonate them can indicate that anyone using their UA Username or ID # will be required by the Identity Provider to use 2-factor authentication. If you invoke this option for your UA identity, anyone attempting to authenticate as you will need not only your UA Username or ID # and your UA Password but access to your registered phone in order to provide the second factor, thus making such impersonation more difficult and less likely.
Implementation
UA IAM is currently (2014Q1) working with Duo Security to provide this capability for two-factor authentication. We have deployed a proof of concept in a non-production environment that demonstrates the integration with some production services. Interested UA members may contact iam@… for details and to participate in the pilot.
Implemented contexts using MFA
MCBDuo2FA: Duo Security 2-factor invoked by Multi-Context Broker
Attachments
-
2nd factor login.png
(28.7 KB) -
added by dabantz@… 11 years ago.
IdP_second_factor_login_screen
-
Duo_app_login_request.png
(59.3 KB) -
added by dabantz@… 11 years ago.
Duo_mobile_app_login_request
- 2nd factor login.jpg (38.8 KB) - added by dabantz@… 11 years ago.
- Duo_app_login_request.jpg (33.8 KB) - added by dabantz@… 11 years ago.
- PoC installation steps.pdf (118.3 KB) - added by dabantz@… 11 years ago.
-
Duo_login.png
(35.6 KB) -
added by dabantz@… 10 years ago.
Duo second factor request on UA IdP login
- Manage_portal.png (33.9 KB) - added by dabantz@… 10 years ago.
- Enroll_device.png (40.2 KB) - added by dabantz@… 10 years ago.
-
2FA user experience.png
(90.3 KB) -
added by dabantz@… 8 years ago.
2FA login screens (Figs 1A, 1B, 1C)
-
2FA_user_experience.png
(90.3 KB) -
added by dabantz@… 8 years ago.
2FA login screens (Figs 1A, 1B, 1C)